
7 Signs Your Business Is One Step Away From a Cyberattack
Cyberattacks don’t happen randomly.
They happen because businesses leave doors open—often without realizing it.
The most dangerous part?
Many companies believe they’re secure when they’re actually exposed.
Here are the 7 biggest warning signs your business may be one step away from a cyberattack.
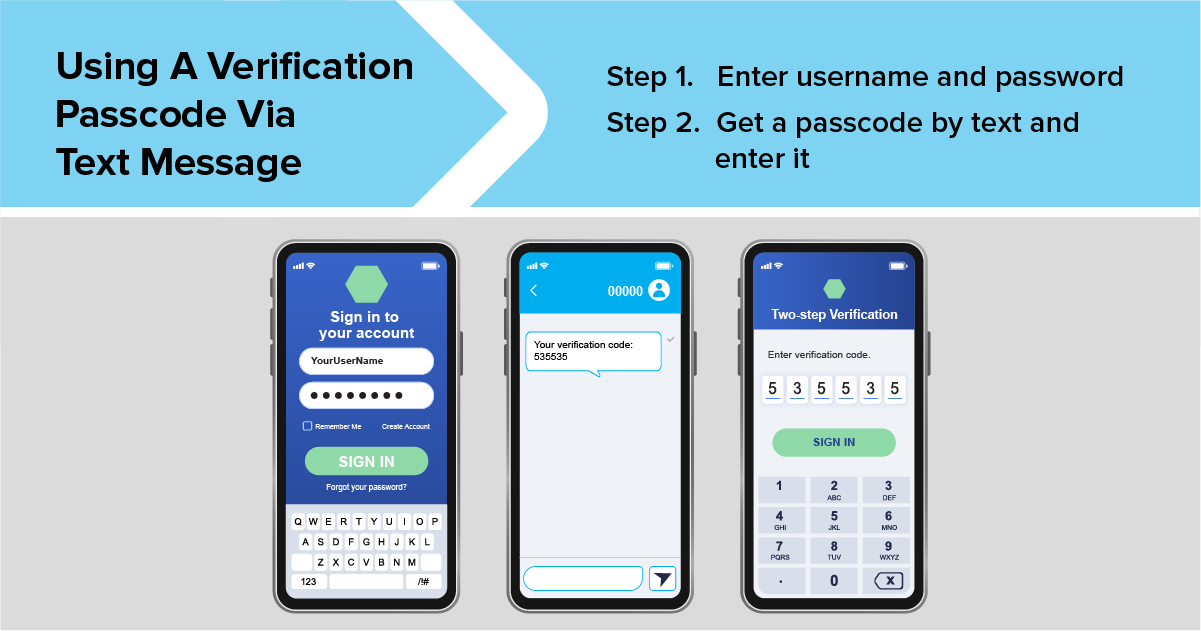
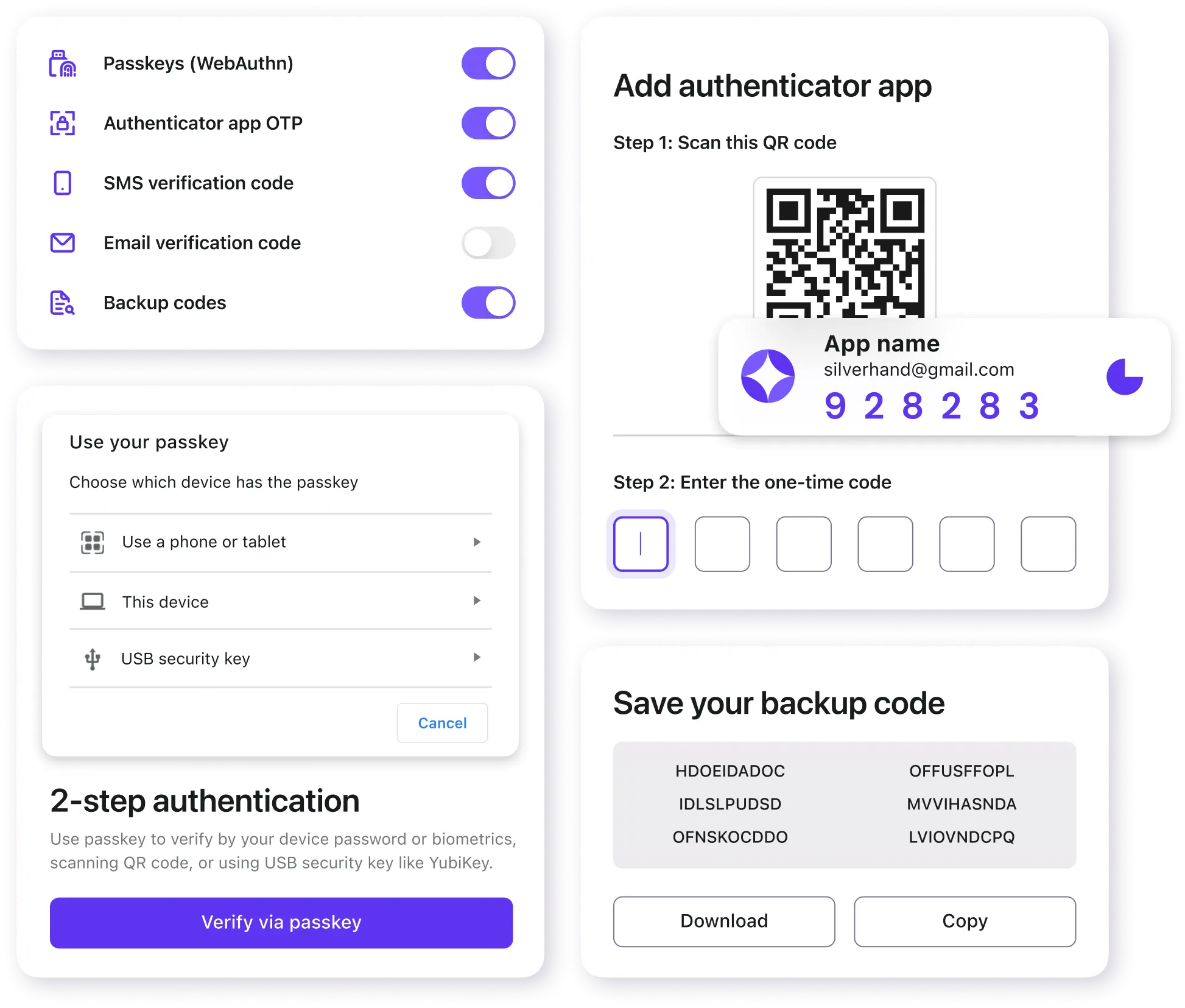
⚠️ 1. No Multi-Factor Authentication (MFA)

4
MFA is your first line of defense.
Without it:
- A stolen password is all an attacker needs
- Email, files, and systems are instantly exposed
👉 This is one of the most common causes of account compromise.
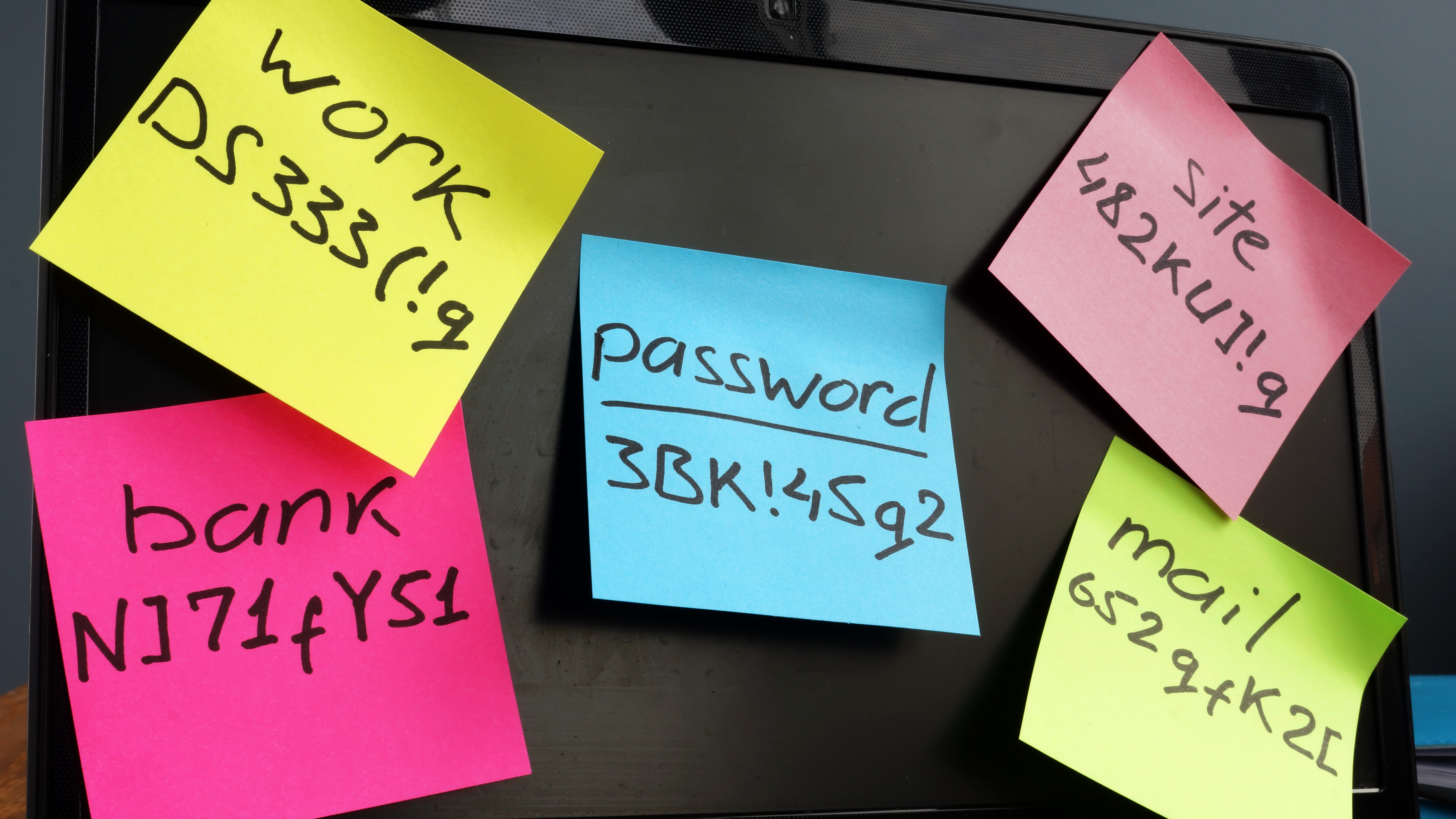
⚠️ 2. Shared Passwords


4
If multiple people share the same login:
- You lose accountability
- You can’t track activity
- You can’t properly secure access
This creates a major security gap.
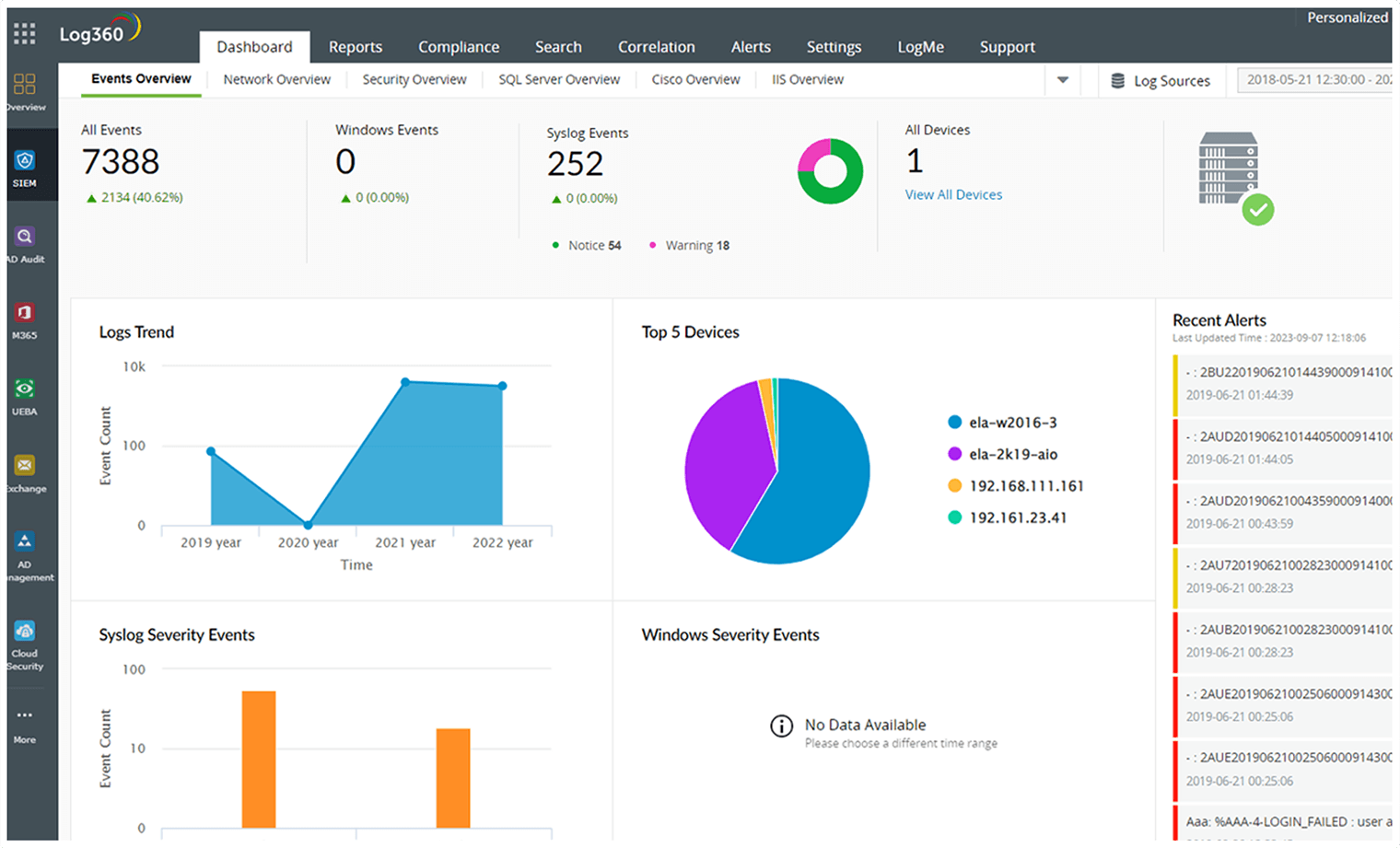
⚠️ 3. No Monitoring


4
Most attacks are not detected immediately.
Without monitoring:
- Threats can sit undetected
- Data can be accessed or stolen quietly
- Damage spreads over time
⚠️ 4. Outdated Systems


4
Outdated systems often contain:
- Known vulnerabilities
- Missing security patches
Attackers actively look for these.
⚠️ 5. No Employee Security Training



4
Your employees are your first line of defense—or your biggest risk.
Without training:
- Phishing emails succeed
- Malicious links get clicked
- Credentials get exposed
⚠️ 6. No Backup Strategy


4
If your data is lost or encrypted:
- Can you recover it?
Without backups:
➡️ You may not recover at all
⚠️ 7. “We Think We’re Secure”


4
This is the most dangerous mindset.
Security is not a feeling—it’s a process.
Without:
- Regular audits
- Proper configurations
- Ongoing monitoring
You’re operating on assumptions.
💥 The Reality
Most cyberattacks don’t target large corporations.
They target:
- Small and mid-sized businesses
- Companies with weak security
- Easy entry points
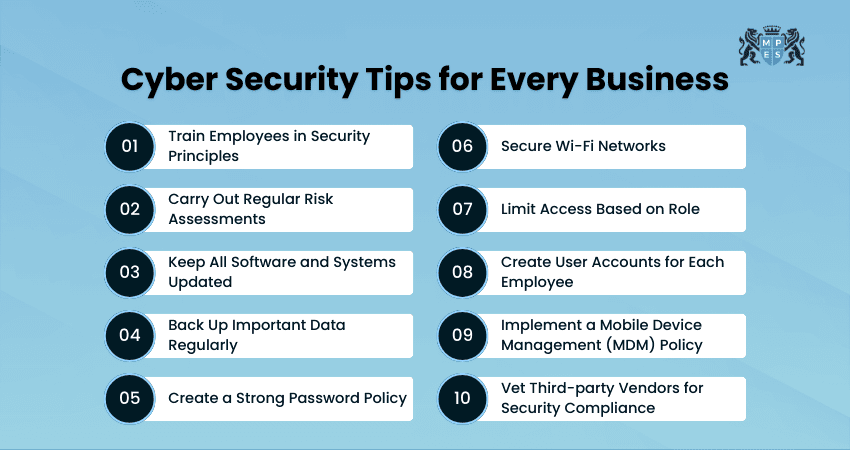
✅ What a Secure Business Looks Like
A properly secured business has:
✔ MFA enforced across all users
✔ Unique credentials (no sharing)
✔ Active monitoring and alerting
✔ Up-to-date systems
✔ Employee security training
✔ Reliable backups
✔ Ongoing security reviews
🧠 Final Thought
Cybersecurity isn’t about reacting.
It’s about preventing problems before they happen.
If even one of these signs applies to your business—you may already be at risk.
📞 Let’s Secure Your Business
At Blackhawk MSP, we:
- Identify vulnerabilities
- Implement protection
- Monitor your environment
So you’re not one step away from a cyberattack—you’re protected against it.
📞 1-925-218-4000
🌐 https://blackhawkmsp.com
